Role-based permissions let you control what users can see and do in your app based on their role, like Admin, Manager, or Viewer. This is crucial for protecting sensitive data and ensuring users only access what they need. In no-code platforms, permissions work on two levels:
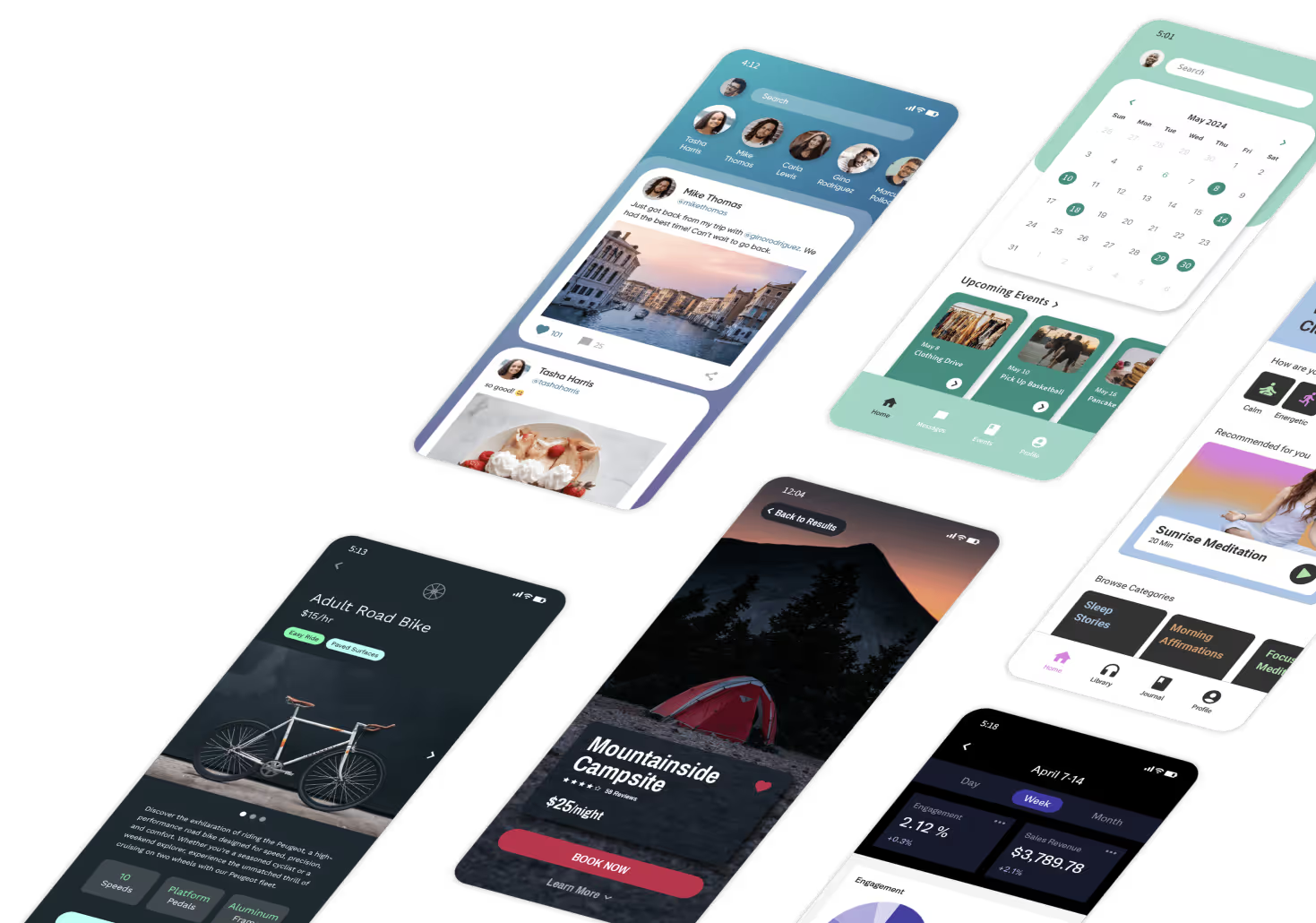
Platforms like Adalo, a no-code app builder for database-driven web apps and native iOS and Android apps—one version across all three platforms, published to the Apple App Store and Google Play, make implementing these permission systems straightforward. With built-in database controls and visual tools, you can configure role-based access without writing code.
- Visibility rules: Hide interface elements users shouldn't see.
- Database permissions: Control who can access or edit data, ensuring security.
To set this up, start by defining roles based on your app's needs (e.g., Admin, Editor, Viewer). Assign permissions carefully - only give users access to what’s necessary. Platforms like Adalo make this easier with tools like "View as User" for testing and layered security controls. Regularly review and update permissions as your app grows to avoid gaps or vulnerabilities.
The key takeaway? Secure your app by combining database-level controls with interface visibility rules and test thoroughly to ensure everything works as intended.

Step-by-step guide to implementing role-based permissions in no-code apps
Defining Roles and Permissions for Your App
When setting up roles for your app, start by aligning them with your organization's structure and the different stages of your business processes. Group users based on the tasks they perform—whether they're employees, HR staff, leads, students, or tenants. People with similar responsibilities typically require similar levels of access. This foundational step creates clear, effective role definitions that scale as your app grows.
Identifying Key Roles and Responsibilities
Most apps benefit from a few standard role tiers that serve as a starting point:
- Admin: Full control, including managing users, settings, and data deletion capabilities.
- Editor or Manager: Responsible for creating and updating content but without access to system-level controls.
- Standard User: Focused on entering personal data and viewing tasks assigned to them.
- Viewer: Limited to read-only access, often for reporting purposes.
- Guest: Can browse public content without authentication.
Assign each role only the permissions necessary for its specific tasks. This approach minimizes security risks if an account is ever compromised. For users who need to take on multiple roles, ensure the system accommodates overlapping permissions. Roles should evolve as your app grows and as team members take on new responsibilities.
Mapping Permissions to Roles
Once roles are defined, assign specific permissions to each one. Start by setting database-level permissions (also known as Collection Permissions). This ensures sensitive data is protected at the source, preventing unauthorized access—not just hiding it in the app's interface.
For example, in a collection like "Users", you can control who can view or edit sensitive fields such as email addresses, phone numbers, or salary details. To strengthen security, link records directly to the relevant user. Combine these database rules with UI visibility settings for a layered approach.
When assigning permissions, use allowlisting—explicitly define what actions are permitted. This is more secure than blocking certain actions, as blocklists can sometimes be bypassed through unexpected vectors.
Documenting Roles and Permissions
Proper documentation is crucial for managing roles and permissions effectively. When creating roles in your app builder, include internal descriptions to explain why specific permissions were granted. As Noloco emphasizes, "Document decisions: Keep track of permission logic."
Regularly review and update this documentation to streamline your system. Overly complex permission rules can slow down performance and make maintenance difficult. Schedule quarterly audits to remove unnecessary permissions and adjust for organizational changes. To reduce errors during role assignment, use dropdown menus for role selection within your app—this ensures consistency and accuracy as your team grows.
Setting Up Role-Based Permissions in Adalo
Adalo, an AI-powered app builder, takes a two-layered approach to secure your app data. Collection Permissions handle access at the database level, while Visibility Rules dictate what users can see in the interface. This setup ensures that simply hiding a button doesn't guarantee the underlying data is secure—true protection happens at the database layer.
Start by setting up user authentication and roles. Add a Role property to your Users collection. You can use a text field for roles (like Admin, Editor, Viewer) or a yes/no toggle for simpler setups (e.g., Is Admin?). For more complex role structures, create a separate "User Roles" collection and link it to your Users collection—a common practice when you build a client portal. This allows for cascading permissions across a hierarchy.
Ada, Adalo's AI builder, lets you describe what you want and generates your app. Magic Start creates complete app foundations from a description, while Magic Add adds features through natural language.
You can automate role assignments during signup by using hidden form fields or onboarding buttons. With Adalo's Magic Start feature, you can describe your app's permission requirements in plain language, and the AI generates your database structure with appropriate role fields already configured. Authentication tokens expire every 20 days, requiring users to log in again for security purposes.
Configuring Database Access Controls
To set database access permissions, open the Database Records popup and click the Shield and Key icon. For the Users collection, Adalo automatically limits access to sensitive fields like Email, Password, and Full Name to "Only the Record Creator." For other collections, use the three-dot menu next to Database Collections to define permissions for creating, viewing, updating, or deleting records.
Your permission options include:
- Everyone
- All Logged-In Users
- Some Logged-In Users
- Nobody
If you choose "Some Logged-In Users", you gain more granular control. However, this requires setting up a relationship property linking the collection to the Users collection. Note that these relationship-based permissions are limited to a depth of two. With Adalo's unlimited database records on paid plans, you can implement complex permission hierarchies without worrying about hitting storage caps or incurring usage-based charges.
Using Adalo's Visual Builder for Role Management
To manage roles visually, set a component's visibility to "Sometimes Visible" based on conditions like:
Logged In User > Role > Is Equal to > [Role Name]
For sensitive actions, dive into "Show Advanced" settings to ensure actions are triggered only by users with the appropriate role. Once you save changes, permissions update instantly, making it easy to adjust access as your team or app evolves.
Adalo's Magic Add feature accelerates this process—describe the permission logic you need in natural language, and the AI configures visibility rules and action conditions automatically. This AI-assisted approach reduces setup time from hours to minutes while maintaining security best practices.
Managing Permissions for Complex Use Cases
Managing Multi-Organization Applications
For those building a no-code SaaS platform serving multiple organizations, keeping data isolated is critical. This builds on the basics of role-based access control (RBAC). Each sensitive record should be linked to its corresponding organization. When users log in, they should only see records where the record's OrganizationID matches their own OrganizationID.
To make this work, include an "Organization" property in the Users collection during signup. Automate this step by using hidden form fields that assign the correct organization ID at the time of registration. Once this is set up, adjust Collection Permissions to "Some Logged In Users" for collections containing organization-specific records. This option becomes available once you've established a relationship between the collection and the Users collection.
Always test your setup using the "View as User" feature to ensure no data is visible across tenants. Adalo's modular infrastructure supports apps with millions of monthly active users, making it suitable for multi-tenant SaaS applications that need to scale without performance degradation.
Setting Up Resource-Specific Permissions
Taking permissions a step further, resource-specific controls allow you to manage access at a more granular level—such as individual records or fields. For instance, a sales representative might only view accounts within their territory, while HR staff could access salary details hidden from others.
Start by defining CRUD (Create, Read, Update, Delete) rights for each role at the collection level. Always begin with the least amount of access necessary. Make sure sensitive collections are linked to the Users collection to enable the "Some Logged In Users" permission logic.
"Permissions are not a replacement for visibility rules. Permissions are database related and visibility rules are design-related. The two should be thought of completely separately and implemented individually." - Adalo Resources
To handle users with overlapping roles, use initial workflow conditions. Also, assign a default role, such as "Guest" or "Standard", to every new user during signup to avoid any gaps in permissions. Unlike platforms that charge based on database operations or impose record limits, Adalo's $36/month plan includes no caps on actions, users, records, or storage—so complex permission structures don't translate to unpredictable costs.
Maintaining and Auditing Access Control
Regular Reviews and Audits
Keeping permissions up to date is an ongoing task. Roles change, employees leave, and new features reshape access needs. To stay ahead, plan quarterly reviews of access permissions. Look for accounts no longer in use, outdated roles, or mismatched permissions that don't align with current job duties.
Adalo enforces automatic re-authentication every 20 days as authentication tokens expire. While this adds a layer of security, manual audits remain crucial. Apps handling sensitive data or serving multiple organizations should integrate an Identity Provider to streamline role updates. By automating compliance checks and clarifying permission structures, you could cut audit time in half.
Emerging AI tools are stepping in to monitor for unusual activity—like unauthorized downloads—and can suggest role adjustments when needed. Routine audits not only catch security gaps but also ensure your app's roles stay aligned with its growth.
Updating Roles as Your App Grows
After each audit, adjust roles to reflect new access requirements. As your app evolves, new features often introduce fresh data sets that need tailored permissions. Define these access rules before launching those features.
Whenever possible, rely on centralized role management through an Identity Provider. This ensures updates propagate instantly across all systems, eliminating the need for manual changes or republishing.
Document every permission change, including what was modified, when, and why. This creates a reliable audit trail and simplifies onboarding for new team members. As your user base expands, revisit the principle of least privilege—more access doesn't always mean better security. Keeping permissions tight ensures your app stays both functional and secure.
With Adalo processing 20 million+ daily requests with 99%+ uptime, your permission system needs to be robust enough to handle scale. The platform's infrastructure maintains performance even as your user base grows from hundreds to millions.
Comparing Permission Capabilities Across Platforms
When choosing a platform for role-based permissions, consider both the technical capabilities and the pricing implications of scaling your permission system.
| Platform | Starting Price | Native Mobile Apps | Database Limits | Usage-Based Charges |
|---|---|---|---|---|
| Adalo | $36/mo | Yes (iOS + Android) | Unlimited | None |
| Bubble | $69/mo | No (web only) | Hard limits | Workload Units |
| Glide | $25/mo | No | Limited | Row limits |
| Softr | $59/mo+ | PWA only ($167/mo) | Scales with plan | User-based |
| FlutterFlow | $80/mo/seat | Yes | No database included | Per-seat |
For apps with complex permission structures, database limits matter significantly. Each role assignment, organization relationship, and permission rule creates database records. Platforms with record caps or usage-based pricing can make multi-tenant permission systems expensive to operate. Adalo's approach—no caps on records or storage—means your permission architecture doesn't drive up costs as you scale.
The ability to publish native iOS and Android apps also affects permission implementation. Native apps can leverage device-level security features and provide faster, more responsive permission checks compared to web-based solutions wrapped in WebViews.
Conclusion
When dealing with real user data, role-based permissions are essential. They ensure your app stays secure while allowing it to grow without compromising sensitive information. Without proper permissions, you risk either locking users out unnecessarily or exposing data to the wrong people.
Start by defining the roles that fit your app's needs—like Admin, Editor, or Viewer—and map out what each role can and cannot do. This step should come early in development to avoid headaches later. From there, layer your security: set database-level collection permissions to protect data on the server side, configure page-level access controls, and use visibility rules to refine the user experience. Remember, hiding a button isn't enough—your data restrictions must back up any UI changes.
Testing is non-negotiable. Use the platform's "view as" feature to test each role with separate accounts and confirm that permissions are working as intended. Once your app is live, make it a habit to audit permissions regularly. Remove old accounts and adjust roles to match your app's growth.
AI is already transforming security, with tools that can flag unusual activity and suggest role adjustments automatically. Even so, manual checks remain essential—especially for apps handling sensitive or regulated data or serving multiple organizations. By combining these practices with ongoing oversight, you can keep your app secure while scaling confidently.
Related Blog Posts
- GDPR and Data Sync in No-Code Apps
- Role-Based Access Control in No-Code Apps
- Role-Based Permissions for Internal Tools
- Managing Sensitive Data in No-Code Apps
FAQ
Why choose Adalo over other app building solutions?
Adalo is an AI-powered app builder that creates true native iOS and Android apps from a single codebase. Unlike web wrappers, it compiles to native code and publishes directly to both the Apple App Store and Google Play Store. At $36/month with unlimited database records and no usage-based charges, it offers predictable pricing that competitors like Bubble ($69/mo with Workload Units) can't match.
What's the fastest way to build and publish an app to the App Store?
Adalo's drag-and-drop interface combined with AI-assisted building through Magic Start and Magic Add lets you go from idea to published app in days rather than months. Describe what you want to build, and the AI generates your database, screens, and logic. Adalo handles the complex App Store submission process, so you can focus on features instead of certificates and provisioning profiles.
What's the difference between visibility rules and database permissions?
Visibility rules control what interface elements users can see in your app, while database permissions control who can actually access or edit the underlying data. Both are essential—hiding a button isn't enough to secure sensitive data, so you need database-level permissions to truly protect information from unauthorized access.
How do I manage permissions for multi-organization apps?
Link each sensitive record to its corresponding organization and configure Collection Permissions to "Some Logged In Users" based on organization relationships. When users log in, they'll only see records matching their OrganizationID, keeping data isolated between tenants. Always test with the "View as User" feature to verify isolation.
How often should I audit role-based permissions?
Plan quarterly reviews of access permissions to catch outdated roles, unused accounts, or mismatched permissions. Adalo enforces automatic re-authentication every 20 days, but manual audits remain essential—especially for apps handling sensitive data or serving multiple organizations.
What roles should I define for my app?
Most apps benefit from standard role tiers: Admin (full control), Editor/Manager (content management), Standard User (personal data entry), Viewer (read-only access), and Guest (public browsing). Assign each role only the permissions necessary for its specific tasks to minimize security risks if an account is compromised.
Which is more affordable for role-based permissions, Adalo or Bubble?
Adalo at $36/month is significantly more affordable than Bubble at $69/month. More importantly, Adalo includes unlimited database records with no usage-based charges, while Bubble imposes hard limits and Workload Units that can drive up costs as your permission system scales with more users and organizations.
Can I migrate my existing app's permissions to Adalo?
Yes, you can recreate your permission structure in Adalo using its visual builder and database controls. The platform's Magic Add feature can help—describe your existing permission logic in natural language, and the AI configures visibility rules and action conditions automatically, reducing migration time significantly.
Do I need coding experience to set up role-based permissions?
No coding experience is required. Adalo's visual builder lets you configure Collection Permissions through a point-and-click interface, and visibility rules use simple conditional logic. The AI-assisted features can even generate permission configurations from plain language descriptions of what you need.
How does Adalo handle permission performance at scale?
Adalo's modular infrastructure processes 20 million+ daily requests with 99%+ uptime and supports apps with millions of monthly active users. Permission checks happen at the database level, so they remain fast even as your user base grows—unlike web wrappers that can slow down under load.